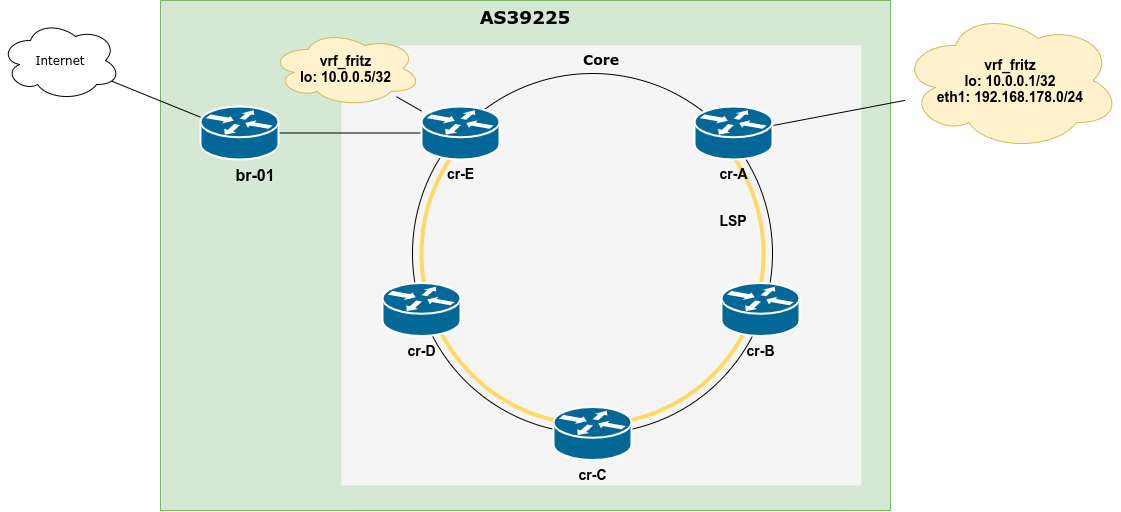
The use of dynamic routing protocols – mainly IS-IS, OSPF and BGP – is quite common in contemporary networks, even on the host networking stacks. In some situations, it is desirable to not only control the path packets will take to any given destination, but also the source address of locally sourced traffic.
By default, Linux systems will use the primary IP address of the egress interfaces, which has global scope and has the same address family as the flow in question. This decision can be overridden per destination by setting the src attribute of a route to a specific locally configured IP address, for example:
ip route add 2001:db8:0815::/48 via 2001:db8:1::1 src 2001:db8::42
For routes installed by a routing daemon, this has to happen inside the routing daemon, so the NETLINK call will know about the source address to set. For bird this is rather straight forward, for FRR it took me – and apparently others – a bit of time to find the right knobs, so I’ll document both ways here for future me and – likely – present you looking for it 🙂
bird
In bird, that’s fairly simple and can be done via the export filter of a protocol kernel. In bird 1 this could look like this:
define LO_IP = 192.0.2.42;
protocol kernel {
scan time 20;
import none;
export filter {
# <Apply any required filtering here/>
# Set src attr of all routers installed in FIB to LO_IP
krt_prefsrc = LO_IP;
accept;
};
}
For bird 2, this has to happen inside the address family specific configuration:
define LO_IP = 2001:db8::42;
protocol kernel {
scan time 20;
ipv6 {
import none;
export filter {
# <Apply any required filtering here/>
# Set src attr of all routers installed in FIB to LO_IP
krt_prefsrc = LO_IP;
accept;
};
}
FRR
For FRR, the configuration is a little bit more involved and requires a route-map to be applied to the protocols the routes are learned from! So if you want to set the source address for routes learned from OSPF this would look like this:
route-map set-loopback-src-ip permit 1
set src 192.0.2.42
!
ip protocol ospf route-map set-loopback-src-ip
If you want to filter on which prefixes this applies, this could be done by adding a prefix list into the route-map, e.g.
route-map set-loopback-src-ip permit 1
match ip address prefix-list YOUR_PREFIX_LIST
set src 192.0.2.42
If you run OSPF + BGP and want the source address to be set for both protocols, you need to add a line to the config example from above:
ip protocol bgp route-map set-loopback-src-ip